In the first blog about the Microsoft Intune App-layer protection, one of the supported features is that you are able to wrap your own applications with the Microsoft Intune App Wrapping Tool for iOS so that you are able to manage those applications with the Mobile Application Management policies. In this second blog in the series, we will have a look at the Microsoft Intune App Wrapping Tool for iOS.
To get a Win32 apps deployed via the Intune Management Extension we first need to package the content we want to distribute. Microsoft decided to use the same approach like they did for the macOS world, where they provide a small tool to create the packages – Microsoft Intune App Wrapping Tool for macOS. A similar tool to create these. Start your free week with CBT Nuggets. This video, Anthony Sequeira covers Microsoft Intune and how you can use it to deploy apps.
With this blog I want to show two scenarios. One with an application with no policies active and one with the same application that is wrapped with the Microsoft Intune App Wrapping Tool with the mobile application policies active. To be able to do this I have created a very basic application with two “pages” and on each page, there is a text field where I can type text and copy and paste it within the application and beyond.
The Intune Windows App (.IntuneWin – “Remote Desktop Connection Manager.intunewin”) created in the above section. Now, you can upload the InutneWin packages to Intune and deploy this bundled app as Intune Windows Apps. Intune Windows App model is similar to SCCM application model. But, Intune app model is a subset of SCCM app model from a. See full list on docs.microsoft.com.
Meet Notepad 🙂
Page 2 of Notepad |
Again it is a very basic and uggly app, but it does its work 🙂 (Okay I will try to make it more fancy 😉 )
That being said, when looking at the Microsoft Intune App Wrapping Tool for iOS, you need to be sure that the following prerequisites are in place:
- You need to have an Apple Developer Account
- You need to have access to a Mac OS X 10.8.5 or later with xcode
- You need to have a Provisioning Profile
- You need to have a distribution certificate
- Your device needs to be based on iOS 7.01 or later
- A developed iOS LOB Application.
Unmanaged Application
So when deploying the standard application via Microsoft Intune, you are able to install it and copy and paste the “Super secret text” between the pages in the Notepad application and for instance the email application within the iOS device.
Create a managed application
So the default created application can be deployed without any problem. What we need to do next is to wrap the Notepad application with the Microsoft Intune App Wrapping Tool to allow management via Microsoft Intune.
You can download the Microsoft Intune App Wrapping Tool for iOS supporting the right language here. Next you need to extract the DMG file to a folder where you are able to access the IntuneMAMPackager tool, TechNet describes to start the command line tool like this ./IntuneMAMPackager.app/Contents/MacOS/IntuneMAMPackager but I also extracted the content from the file to be able to access the IntuneMAMPackager file directly.
The IntuneMAMPackager tool has the following parameters that you may need to add to be able to wrap your application.
| Parameter | Description |
| -i | The path and file name of the source application. (mandatory) |
| -o | The path in which to save the wrapped application. (mandatory) |
| -p | The path of your provisioning profile for iOS applications. (mandatory) |
| -c | The SHA1 hash of the signing certificate (Optional). |
| -a | The Client ID of the input app (in GUID format) if the app uses Azure Active Directory Libraries (Optional). |
| -t | The path to a test mobile application management policy file for testing outside of Intune (Optional). |
| -r | Redirect URI of the input app if the app uses Azure Active Directory Libraries (Optional). |
| -v | Verbose messages while wrapping the application. |
For my Notepad application I need to start the following command line at the console of the Mac OS X device;
./IntuneMAMPackager –i ./Notepad-v1.ipa –p XC_Ad_Hoc_.mobileprovisioning –o ./Notepad- wrapped.ipa –c 679cd10b63499c3f89c6edfb07d2e2b80dfb0d
Application wrapped by the Microsoft Intune App Wrapping Tool
That you cannot wrap every IPA file is true since the wrapping tool cannot wrap the following apps;
- Encrypted apps
- Unsigned apps
- Apps with extended file attributes
Trying to wrap an app that is not signed by Apple
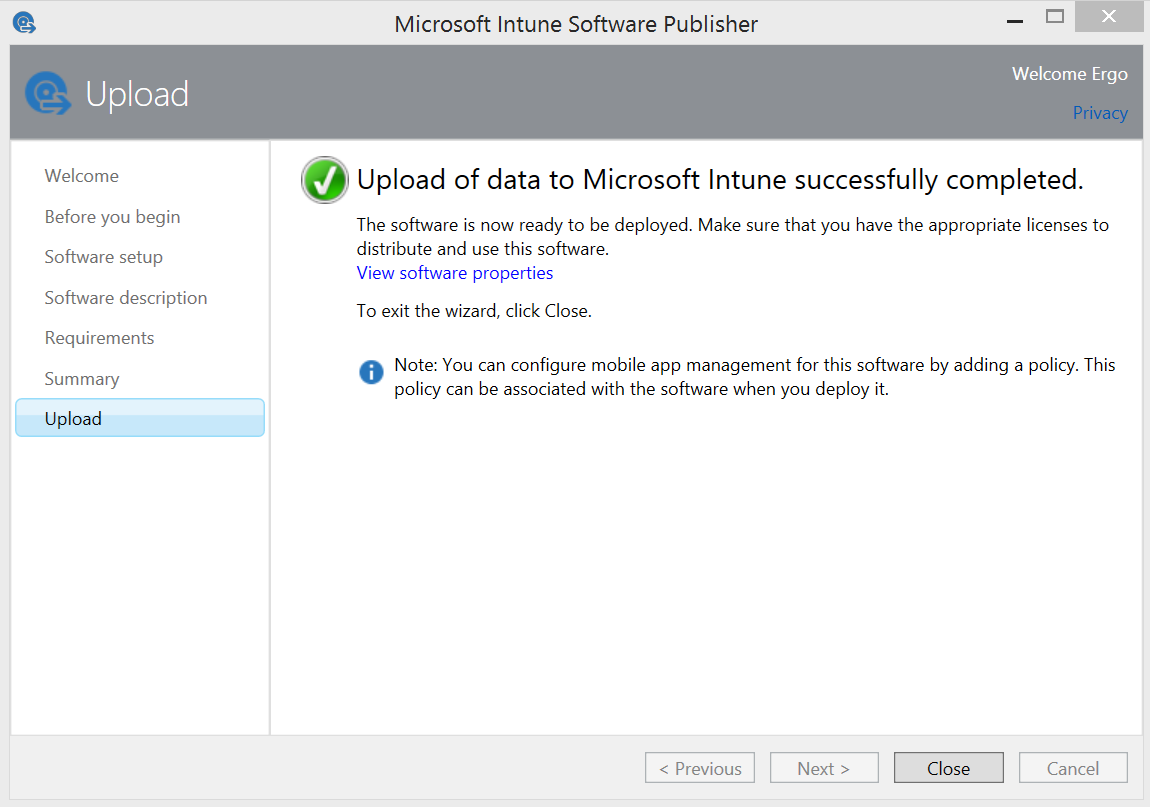
In the next blog we will add the application to Microsoft Intune, deploy it and have a look how the Mobile Application Management Policies can be applied to the managed application.
Intune App Wrapping Tool For Android
Till next time.
Comments
-->Use the Microsoft Intune App Wrapping Tool for Android to change the behavior of your in-house Android apps by restricting features of the app without changing the code of the app itself.
The tool is a Windows command-line application that runs in PowerShell and creates a wrapper around your Android app. After the app is wrapped, you can change the app's functionality by configuring mobile application management policies in Intune.
Before running the tool, review Security considerations for running the App Wrapping Tool. To download the tool, go to the Microsoft Intune App Wrapping Tool for Android on GitHub.
Note
If you have issues with using the Intune App Wrapping Tool with your apps, submit a request for assistance on GitHub.
Fulfill the prerequisites for using the App Wrapping Tool
You must run the App Wrapping Tool on a Windows computer running Windows 7 or later.
Your input app must be a valid Android application package with the file extension .apk and:
- It cannot be encrypted.
- It must not have previously been wrapped by the Intune App Wrapping Tool.
- It must be written for Android 4.0 or later.
The app must be developed by or for your company. You cannot use this tool on apps downloaded from the Google Play Store.
To run the App Wrapping Tool, you must install the latest version of the Java Runtime Environment and then ensure that the Java path variable has been set to C:ProgramDataOracleJavajavapath in your Windows environment variables. For more help, see the Java documentation.
Note
In some cases, the 32-bit version of Java may result in memory issues. It's a good idea to install the 64-bit version.
Android requires all app packages (.apk) to be signed. For reusing existing certificates and overall signing certificate guidance, see Reusing signing certificates and wrapping apps. The Java executable keytool.exe is used to generate new credentials needed to sign the wrapped output app. Any passwords that are set must be secure, but make a note of them because they're needed to run the App Wrapping Tool.
Note
The Intune App Wrapping Tool does not support Google's v2 and upcoming v3 signature schemes for app signing. After you have wrapped the .apk file using the Intune App Wrapping Tool, the recommendation is to use Google's provided Apksigner tool. This will ensure that once your app gets to end user devices, it can be launched properly by Android standards.
(Optional) Sometimes an app may hit the Dalvik Executable (DEX) size limit due to the Intune MAM SDK classes that are added during wrapping. DEX files are a part of the compilation of an Android app. The Intune App Wrapping Tool automatically handles DEX file overflow during wrapping for apps with a min API level of 21 or higher (as of v. 1.0.2501.1). For apps with a min API level of < 21, best practice would be to increase the min API level using the wrapper's
-UseMinAPILevelForNativeMultiDexflag. For customers unable to increase the app's minimum API level, the following DEX overflow workarounds are available. In certain organizations, this may require working with whoever compiles the app (ie. the app build team):- Use ProGuard to eliminate unused class references from the app's primary DEX file.
- For customers using v3.1.0 or higher of the Android Gradle plugin, disable the D8 dexer.
Install the App Wrapping Tool
From the GitHub repository, download the installation file InstallAWT.exe for the Intune App Wrapping Tool for Android to a Windows computer. Open the installation file.
Accept the license agreement, then finish the installation.
Note the folder to which you installed the tool. The default location is: C:Program Files (x86)Microsoft Intune Mobile Application ManagementAndroidApp Wrapping Tool.

Run the App Wrapping Tool
Important
Intune regularly releases updates to the Intune App Wrapping Tool. Regularly check the Intune App Wrapping Tool for Android for updates and incorporate into your software development release cycle to ensure your apps support the latest App Protection Policy settings.
On the Windows computer where you installed the App Wrapping Tool, open a PowerShell window.
From the folder where you installed the tool, import the App Wrapping Tool PowerShell module:
Run the tool by using the invoke-AppWrappingTool command, which has the following usage syntax:
The following table details the properties of the invoke-AppWrappingTool command:
| Property | Information | Example |
|---|---|---|
| -InputPath<String> | Path of the source Android app (.apk). | |
| -OutputPath<String> | Path to the output Android app. If this is the same directory path as InputPath, the packaging will fail. | |
| -KeyStorePath<String> | Path to the keystore file that has the public/private key pair for signing. | By default, keystore files are stored in 'C:Program Files (x86)JavajreX.X.X_XXbin'. |
| -KeyStorePassword<SecureString> | Password used to decrypt the keystore. Android requires all application packages (.apk) to be signed. Use Java keytool to generate the KeyStorePassword. Read more about Java KeyStore here. | |
| -KeyAlias<String> | Name of the key to be used for signing. | |
| -KeyPassword<SecureString> | Password used to decrypt the private key that will be used for signing. | |
| -SigAlg<SecureString> | (Optional) The name of the signature algorithm to be used for signing. The algorithm must be compatible with the private key. | Examples: SHA256withRSA, SHA1withRSA |
| -UseMinAPILevelForNativeMultiDex | (Optional) Use this flag to increase the source Android app's minimum API level to 21. This flag will prompt for confirmation as it will limit who may install this app. Users can skip the confirmation dialog by appending the parameter '-Confirm:$false' to their PowerShell command. The flag should only be used by customers on apps with min API < 21 that fail to wrap successfully due to DEX overflow errors. | |
| <CommonParameters> | (Optional) The command supports common PowerShell parameters like verbose and debug. |
For a list of common parameters, see the Microsoft Script Center.
To see detailed usage information for the tool, enter the command:
Example:
Import the PowerShell module.
Run the App Wrapping Tool on the native app HelloWorld.apk.
You will then be prompted for KeyStorePassword and KeyPassword. Enter the credentials you used to create the key store file.
The wrapped app and a log file are generated and saved in the output path you specified.
How often should I rewrap my Android application with the Intune App Wrapping Tool?
The main scenarios in which you would need to rewrap your applications are as follows:
- The application itself has released a new version. The previous version of the app was wrapped and uploaded to the Intune console.
- The Intune App Wrapping Tool for Android has released a new version that enables key bug fixes, or new, specific Intune application protection policy features. This happens every 6-8 weeks through GitHub repo for the Microsoft Intune App Wrapping Tool for Android.
Intune App Wrapping Tool Download
Some best practices for rewrapping include:
- Maintaining signing certificates used during the build process, see Reusing signing certificates and wrapping apps
Intune App Wrapping Tool Windows 10
Reusing signing certificates and wrapping apps
Android requires that all apps must be signed by a valid certificate in order to be installed on Android devices.
Wrapped apps can be signed either as part of the wrapping process or after wrapping using your existing signing tools (any signing information in the app before wrapping is discarded). If possible, the signing information that was already used during the build process should be used during wrapping. In certain organizations, this may require working with whoever owns the keystore information (ie. the app build team).
If the previous signing certificate cannot be used, or the app has not been deployed before, you may create a new signing certificate by following the instructions in the Android Developer Guide.
If the app has been deployed previously with a different signing certificate, the app can't be uploaded to Intune after upgrade. App upgrade scenarios will be broken if your app is signed with a different certificate than the one the app is built with. As such, any new signing certificates should be maintained for app upgrades.
Security considerations for running the App Wrapping Tool
To prevent potential spoofing, information disclosure, and elevation of privilege attacks:
Ensure that the input line-of-business (LOB) application, output application, and Java KeyStore are on the same Windows computer where the App Wrapping Tool is running.
Import the output application to Intune on the same machine where the tool is running. See keytool for more about the Java keytool.
If the output application and the tool are on a Universal Naming Convention (UNC) path and you are not running the tool and input files on the same computer, set up the environment to be secure by using Internet Protocol Security (IPsec) or Server Message Block (SMB) signing.
Ensure that the application is coming from a trusted source.
Secure the output directory that has the wrapped app. Consider using a user-level directory for the output.